A Secure Key Management Protocol guarantees the security of cryptographic keys throughout their lifecycle. This protocol adopts a set of strategies to produce new keys, archive them securely, and transmit them precisely among authorized parties. The protocol also addresses key rotation to mitigate the risk of violation.
Secure Communication Protocol 26b5a-1c56c-6125a-6ff89-6c087
The protocol 26b5a-1c56c-6125a-6ff89-6c087 is a cutting-edge method for sharing data in an uncrackable manner. This advanced system utilizes cryptography to transform information, making it readable only to authorized parties. By employing layered security protocols, 26b5a-1c56c-6125a-6ff89-6c087 provides a reliable channel for private communication.
- Advantages of using 26b5a-1c56c-6125a-6ff89-6c087 include increased privacy, data integrity, and minimized risk of breaches.
- Implementations for this protocol are diverse, spanning from private communication to critical infrastructure.
Deployment Details for 26b5a-1c56c-6125a-6ff89-6c087
This document outlines the specific implementation specifications for the initiative identifier 26b5a-1c56c-6125a-6ff89-6c087. It provides a thorough overview of the methods employed, the tools utilized, and the expected outcomes. The rollout process is described in phases, each with its unique objectives and artifacts. Communication between stakeholders is emphasized throughout the implementation lifecycle to ensure a smooth transition.
DPOMechanism Analysis of 26b5a-1c56c-6125a-6ff89-6c087 Defense
The protocol 26b5a-1c56c-6125a-6ff89-6c087, a novel system for communicating sensitive data, requires thorough security analysis to guarantee its integrity. This analysis will scrutinize the protocol's architecture and identify potential threats that could be exploited by malicious actors. A multifaceted approach will be employed, including code review, to determine the protocol's protection against various security threats.
Additionally, the analysis will take into account real-world applications to highlight potential points of attack. The goal is to mitigate the risk of security attacks and confirm the confidentiality, integrity, and availability of the data transmitted using this protocol.
Threat Analysis for 26b5a-1c56c-6125a-6ff89-6c087
Performing a in-depth vulnerability assessment on the system with identifier 26b5a-1c56c-6125a-6ff89-6c087 is essential for identifying potential weaknesses. This analysis involves systematically examining the system's configuration to uncover any potential threats that could be exploited by malicious actors. By regularly conducting these assessments, organizations can minimize the risk of compromises, protecting their sensitive data and systems.
Assessment for 26b5a-1c56c-6125a-6ff89-6c087
The detailed performance assessment of the framework 26b5a-1c56c-6125a-6ff89-6c087 highlights its advantages in diverse aspects. The assessment employed a variety of measures to quantify its performance across significant parameters.
- Furthermore, the results demonstrate that the system exhibits efficient operation under diverse scenarios.
- However, there are domains where improvement is necessary to maximize its comprehensive performance.
Overcoming these limitations will contribute in a more reliable and high-performing system.
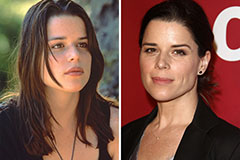 Neve Campbell Then & Now!
Neve Campbell Then & Now! Kelly McGillis Then & Now!
Kelly McGillis Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now! Tina Louise Then & Now!
Tina Louise Then & Now! Erika Eleniak Then & Now!
Erika Eleniak Then & Now!